Many organizations have invested in Splunk Enterprise Security. However, your security strength doesn't with installation. Splunk Enterprise Security allows organizations to combat threats with actionable intelligence and advanced analytics at scale. This helps teams:
- Reduce time to detect
- Streamline investigations
- Achieve faster time to value
However, simply installing the product in your environment doesn't mean that your job is done. It means that your job has just started! Many organization fail to optimize their security posture and the ES software after product implementation. This leads to the following gaps:
- Alert fatigue - too many notifications taking over your daily operations
- Uncertainty on what to prioritize because all security issues look similar
- Lack of optimizing the product to your business needs - it's a large, complex platform that requires time, effort, and knowledge to fully optimize
With over 15 years if experience in the Splunk security space - our team has learned how to improve your security posture in Splunk with efficiency and quality as top of mind. Below we've gathered our top five ways to improve your security posture using Splunk Enterprise Security.
1. Configuring and classifying Assets and Identities
Technology is rarely cookie cutter, something that very much applies to ES Assets and Identities. A solid implementation of A&I is crucial to a successful ES implementation. We at Arcus have had much success leveraging Active Directory data and the SecKit Apps, as well as other data sources such as Crowdstrike, Tenable, and ServiceNow. Besides setting key fields like priority, bunit, identity, nt_host, etc, we also recommend leveraging the multivalued category field (available for both Assets and Identities) to add important information like account type (i.e. privileged, service), OS role, etc.
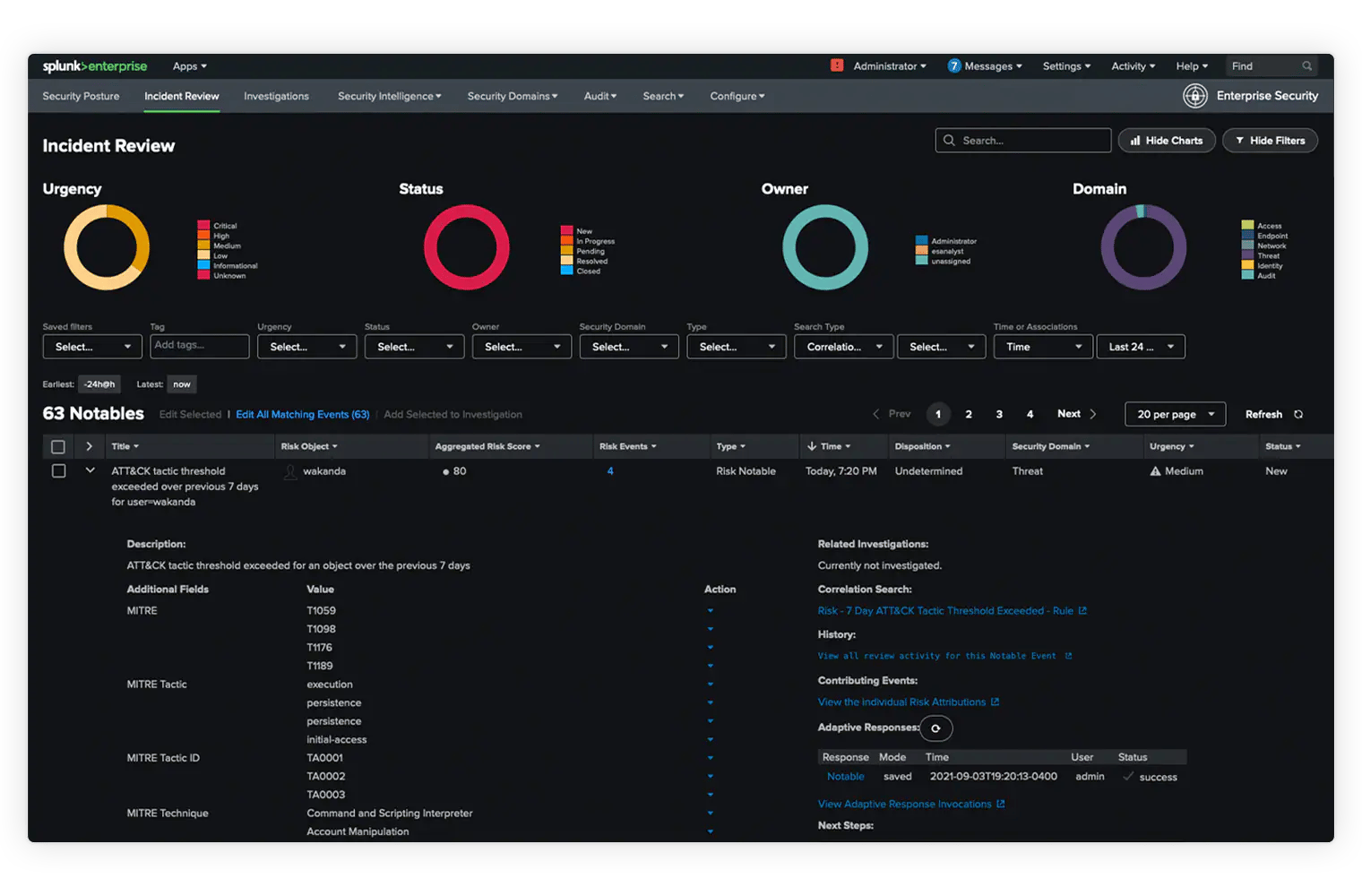
2. Leverage risk-based alerting
Have you ever logged into ES and felt lost and overwhelmed because of all the Notable Events? That's called "alert fatigue" and it's one of your worst nightmares because it's never just one thing that went wrong. This is where Risk-Based Alerting (RBA) comes in - especially with ES versions 7.0 and up. RBA allows you to focus on the important issues because they are the ones causing the most "risk" in your environment. For example, a privileged user who is successfully phished is creates more "risk" than a regular user who is successfully phished. RBA lets you automatically apply Risk Rules to situations like this... just be sure your Assets and Identities are solid! If you also have Splunk SOAR, you can take advantage of a set of freely-available RBA Playbooks as well.
3. Threat Intelligence FeedS
Splunk Enterprise Security has a very capable and configurable Threat Intelligence Framework (TIF) for matching IOC's against security data. However, the quality of the matches is highly dependent on the quality of the IOC's. While ES ships with several pre-configured open source Threat Feeds, in general you will be much happier with a commercial (e.g. Crowdstrike, Infoblox, ThreatConnect, etc) or industry-specific (e.g. E-ISAC) Threat Feed. Keep in mind that some commercial feeds require some work to fully integrate with the TIF.
4. Leverage BUILT-IN Enterprise Security Workflows
ES has two integrated workflows for handling potential incidents: Notable Event Triage and Investigations. Use the first for working high-quality Notable Events that generally standalone such as a phishing alert from your email provider. Use Investigations to document and collaborate with colleagues on more complex incidents that potentially span multiple Notable Events or other alerts.
5. Engage with trusted advisors to help you understand security posture
Splunk Enterprise Security is a large, complex platform that truly benefits from being deployed and configured properly. In order to hit the ground running you should leverage trusted advisors that can help you customize the platform and integrate it into your security organization. This will prevent your team from potentially making costly mistakes when they could be spending more time on actions that drive the business.
questions & resources
If you need any support or have any questions please feel free to contact us at hello@arcusdata.io. Our team has expertise