In this blog series we will be diving into how finding blind spots in your daily and security can help you with your: time, coverage, scheduling and failure detection. In this blog we will uncover how important it is to maintain coverage for the sake of the customer and stakeholder! Don't forget to read the first blog in the series on finding blinds spots to gain insight on how to maintain time.
It's important to maintain coverage regarding your Splunk security operations because it ensures you have all the right data sources. For example, if you are monitoring anti-virus clients you want to make sure that you have a way to ensure that you have them all covered. This is vital because if you are monitoring events and you are only monitoring a partial amount of them then you are missing aspects causing potential major vulnerabilities.
From a security perspective - not having full coverage in SecOps:
- You could miss key security indicators because you’re not monitoring consistently
- It could also give you a false sense of security because you may lack what you think you have
- You could be missing errors/problems that could impact the business and revenue goals
- It's also hard to project growth if you don’t have all of the data to analyze and act
- For example, if you don’t have all the data sources then you don’t know what you’re consuming or have an accurate picture of your resources.
You should check for coverage in the following scenarios:
- Every 6 months for maintenance
- When you are onboarding the data or when bringing on the data sources
- Also when you work with the change management process - you need to check for coverage so you know when a new device is being added/removed
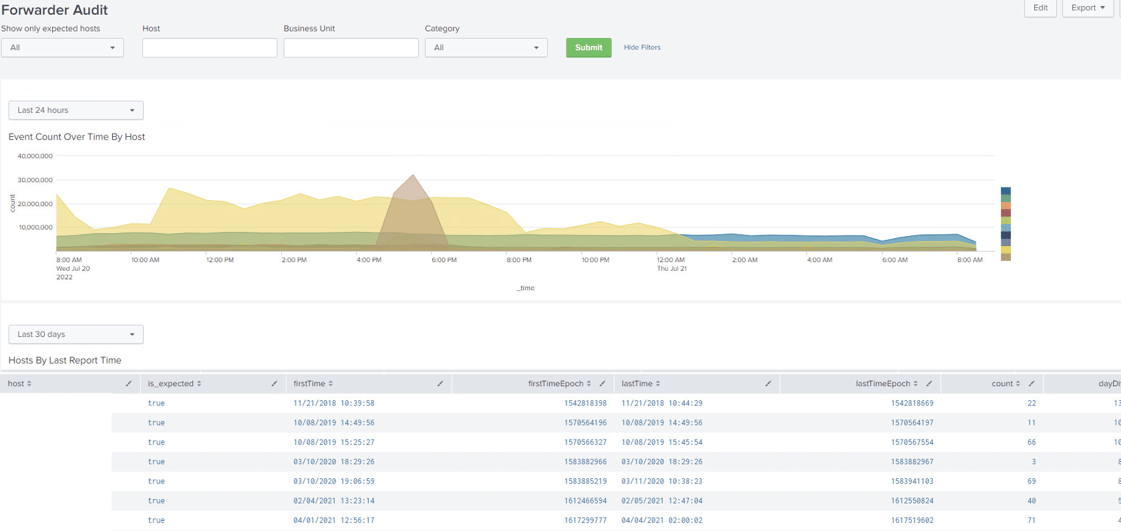
When you check for coverage it's best practice to have a dashboard tor tracking and KPI monitoring. Here is an example of highlighting tracking of Asset Coverage and their status.
However, there are more ways to manage assets via dashboards and reporting to support coverage maintenance.
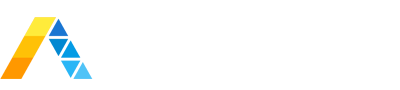
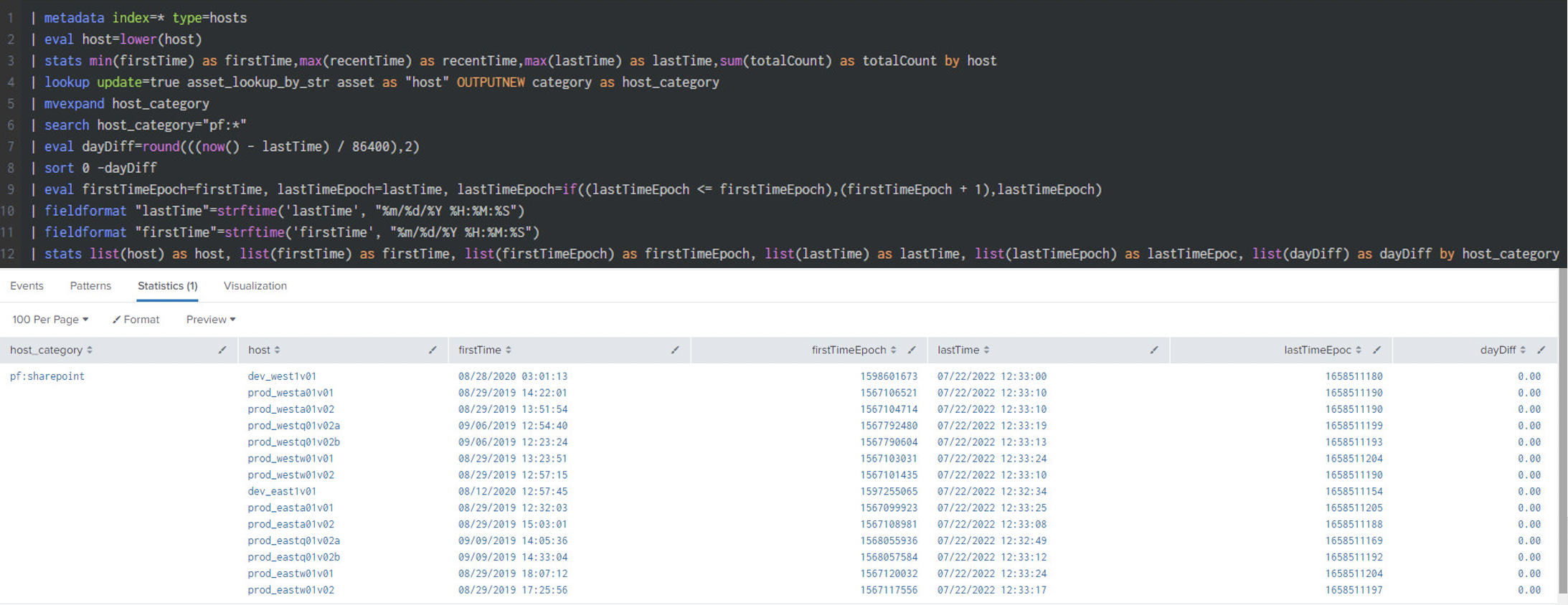
Splunk Enterprise Security (ES) utilizes Asset lookups for managing assets. We often use the “categories” field inside that lookup to classify assets by various attributes. We can use it in our use case here to make sure all of our expected assets are present by utilizing the “Primary Function” (pf:x) attribute we decided to create.
- The search below searches Splunk metadata for all indexes and returns all hosts and when was the first and last time they are seen.
- Then we use the “asset_lookup_by_str” from ES Assets to correlate the host with our Primary Function attribute to group all of our information by Primary Function.
- Now we can save this as a report, include it in a dashboard or even alert when the “dayDiff” is greater than a specific threshold.
- Although we used Splunk ES in our example, you can utilize your own Asset tracking mechanism within Splunk. All you need to do is add a field with a value that can be used to group assets to make sure they are always there.
Here are a few tips to help you with dashboard creation regarding security visibility:
Make a couple of modifications and start creating dashboards to monitor sets of Servers:
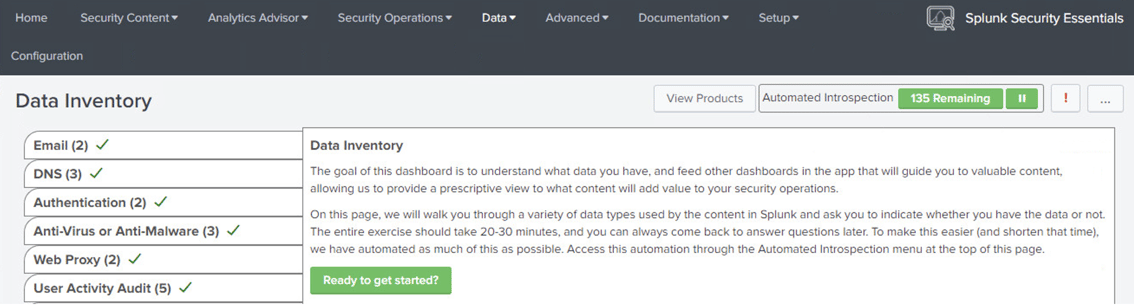
Within the “Splunk Security Essentials” app is the “Data Inventory” dashboard that assists customers in finding and cataloging data sources.
- Note: You can also use Splunk Enterprise Security Assets’ built in functionality to monitor assets and get notifications when any fail to report as expected.
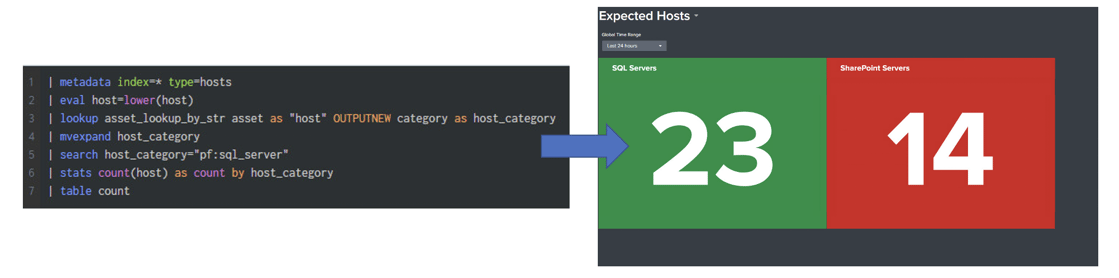
The “Splunk Enterprise Security” app should be used as the “Forwarder Audit” dashboard
We will be providing more tips and expert in this blog series! Don't forget to read the first blog in the series on finding blinds spots to gain insight on how to maintain time.